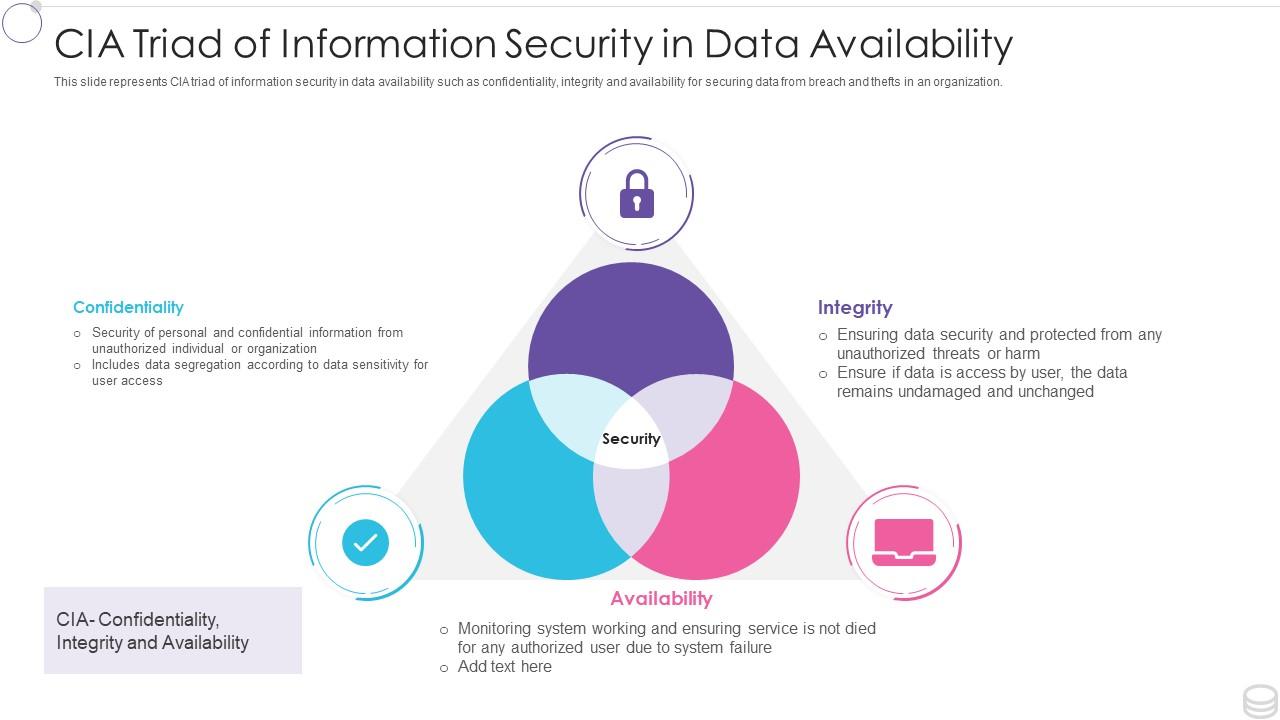
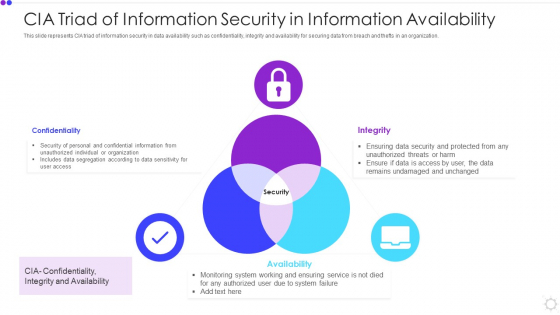
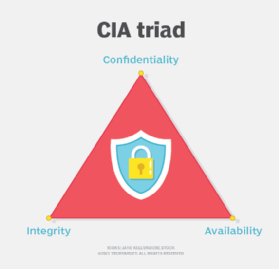
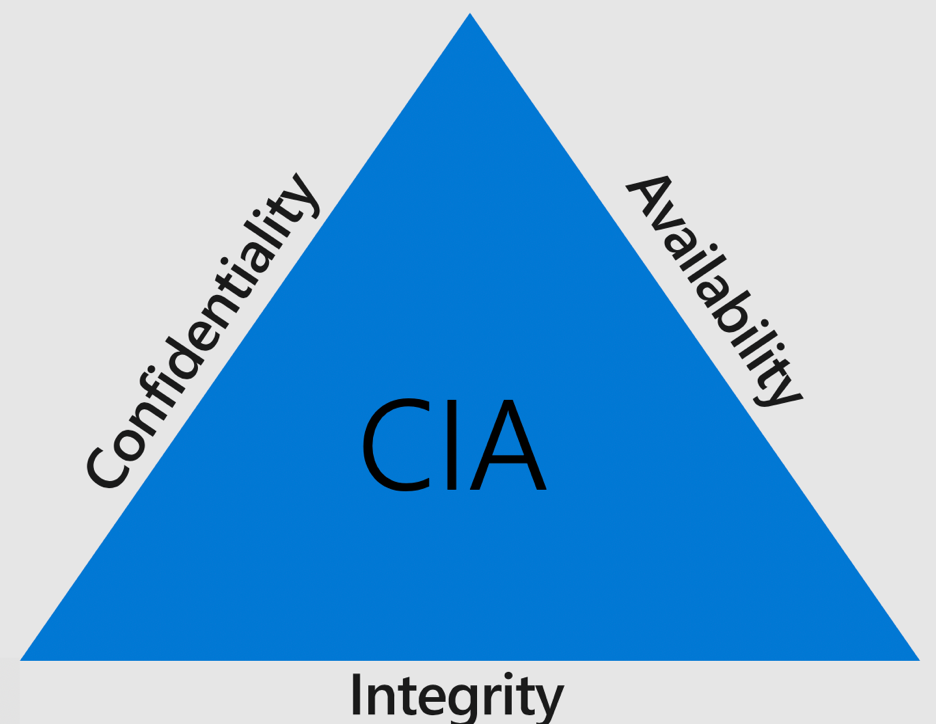
Cia Triad Of Information Security In Data Availability | Presentation Graphics | Presentation PowerPoint Example | Slide Templates
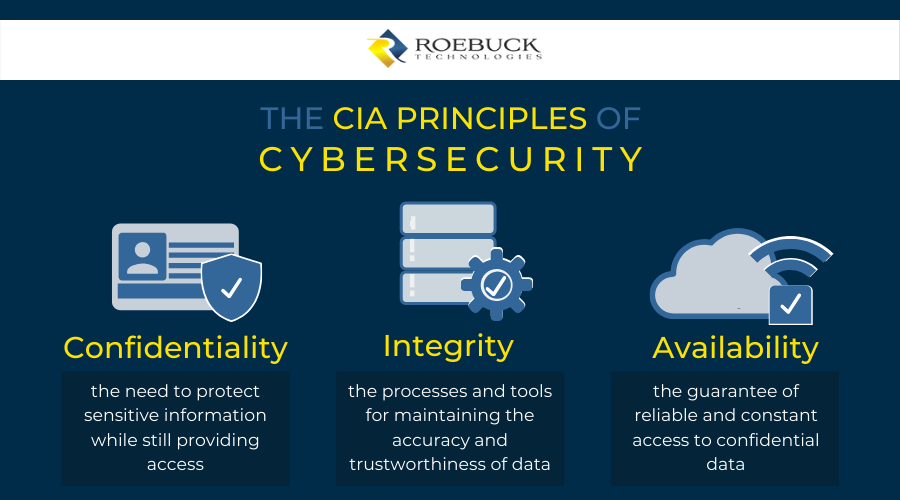
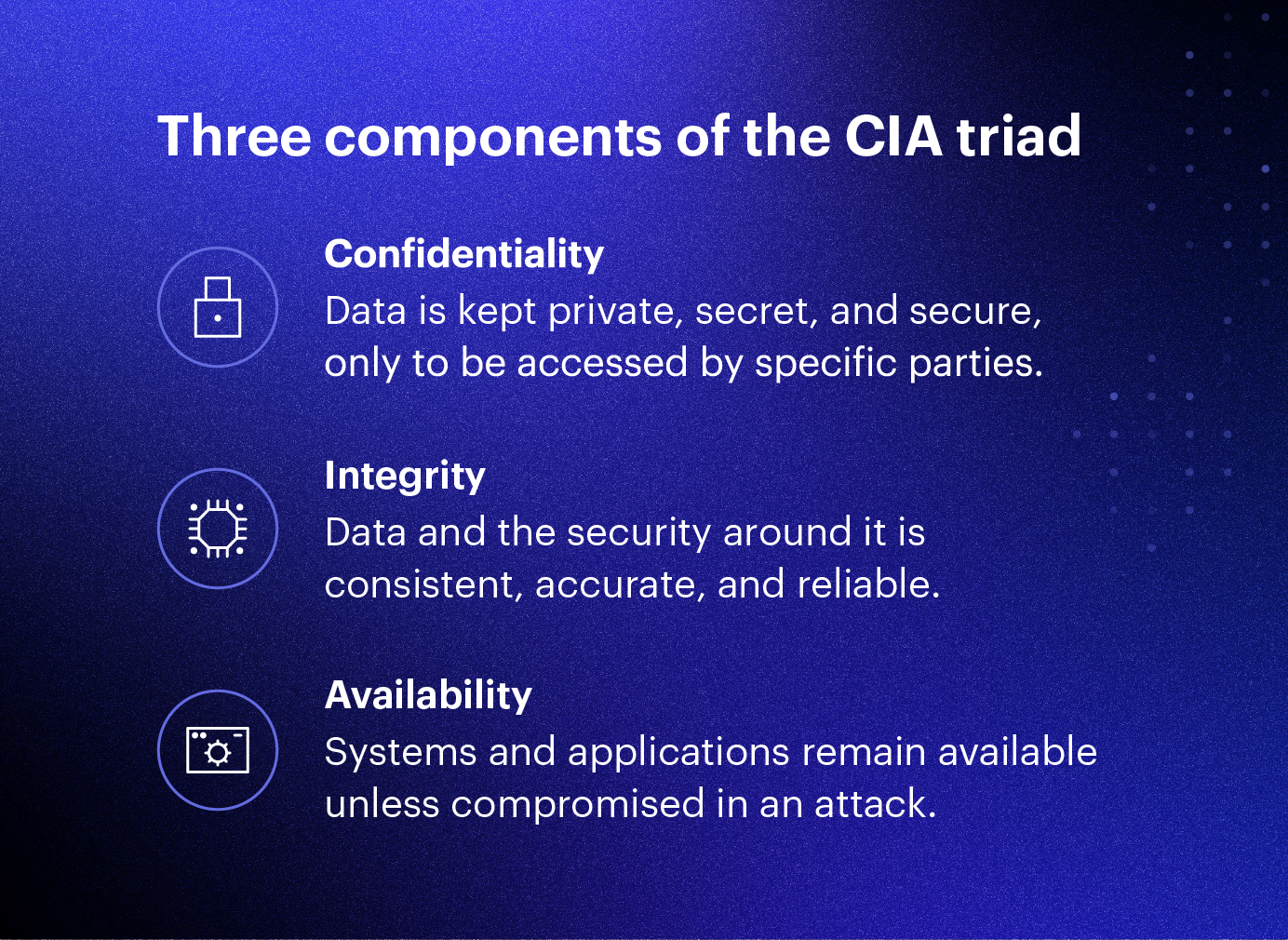
Ensure Confidentiality, Integrity and Availability of corporate data in a distributed workforce - ManageEngine Mobile Device Manager Plus



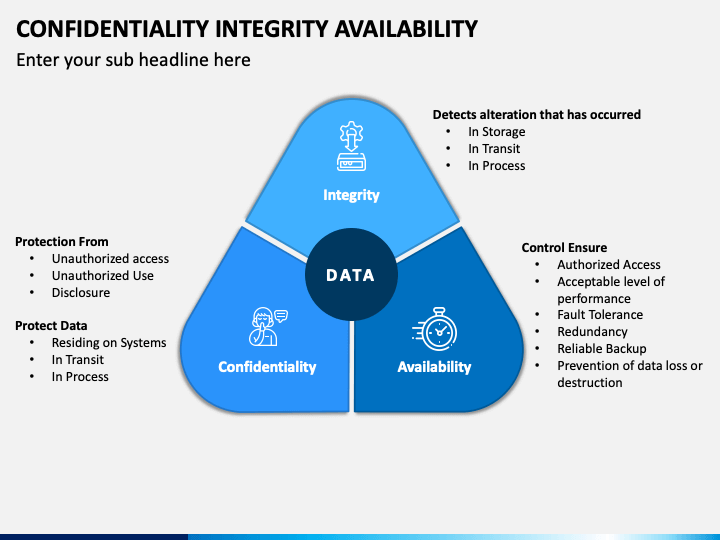


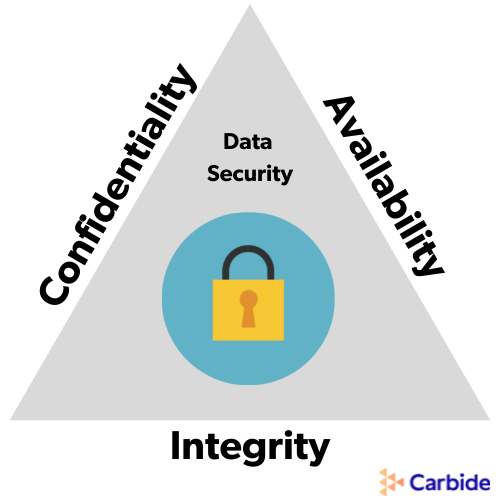

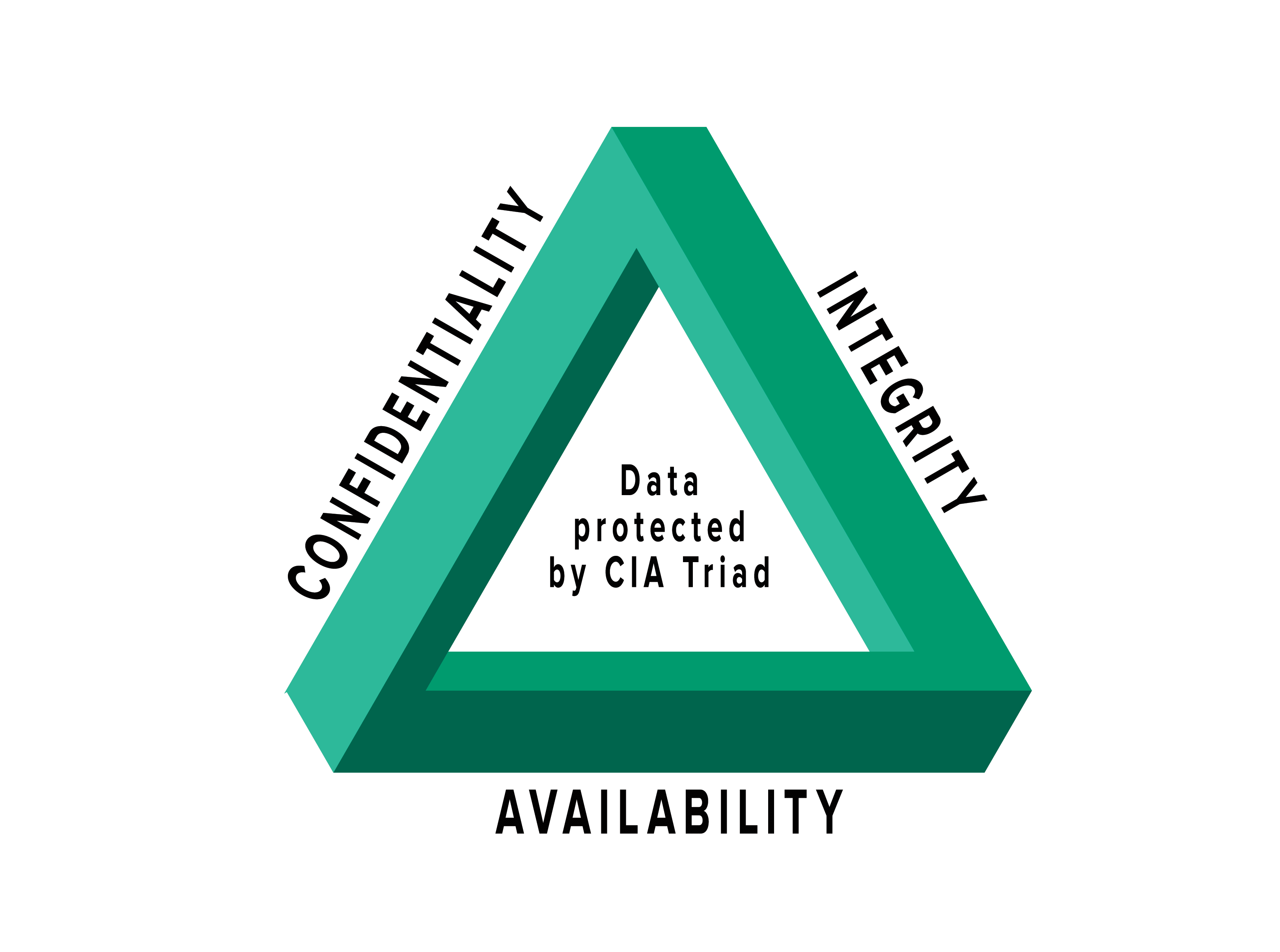
![Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager](https://dataprivacymanager.net/wp-content/uploads/2019/10/Three-pillars-of-information-security-and-cybersecurity.png)

